Search
-
Recent Posts
- PC-3000 SSD Systems. The List of Supported SSDs (regularly updated, ver. 3.7.4)
- PC-3000 SSD. Initio INIC-6081 recovery
- Intel Optane Memory H10 (H20) Series Data Recovery
- RAID technology overview: Proper and Improper Rebuild for RAID-5
- PC-3000 Flash – Noname (CBM2099) USB Recovery. Importance of Translator assembling
Categories
Follow us on Facebook!
Tag Cloud
ACELAB chip ID Data Extractor Data Recovery DE ECC encryption F3 fixing Flash Flash Recovery HDD Heads Hitachi Marvell microSD microSD recovery monolith NAND ocz PC-3000 PC-3000 Flash PC-3000 HDD PC-3000 SSD Plextor RAID RAID Edition recovery ROM SA Samsung Seagate Seagate F3 Soldering SSD SSD Recovery TLC Toshiba Translator unsoldering USB warming WD Western Digital XORLogin / Authorization
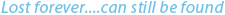
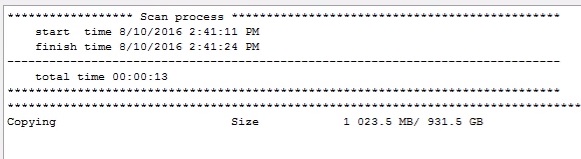
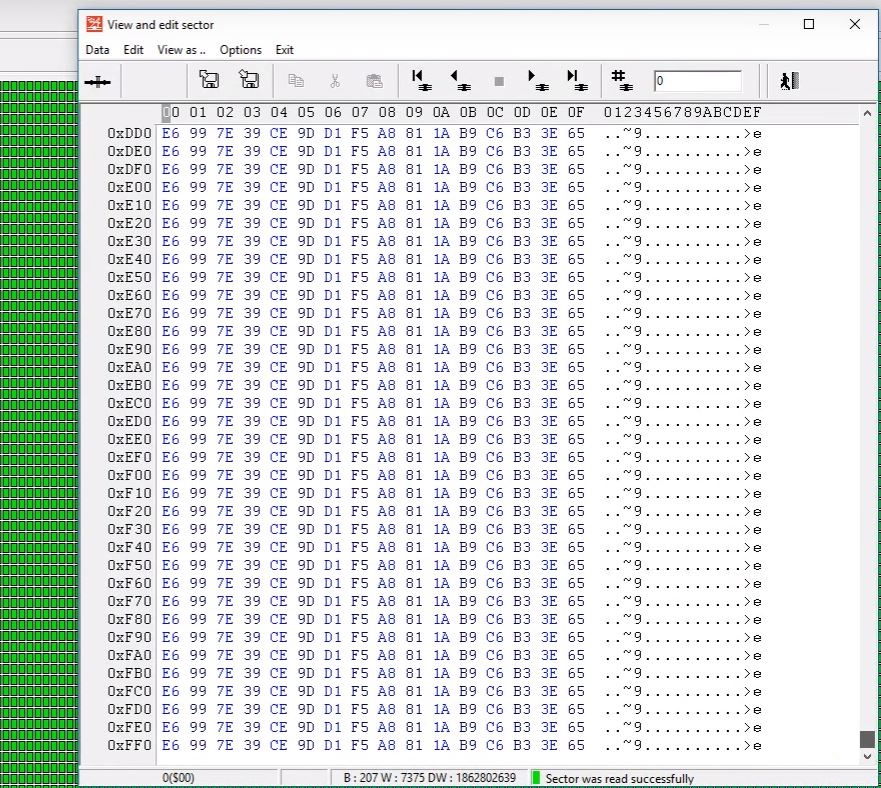
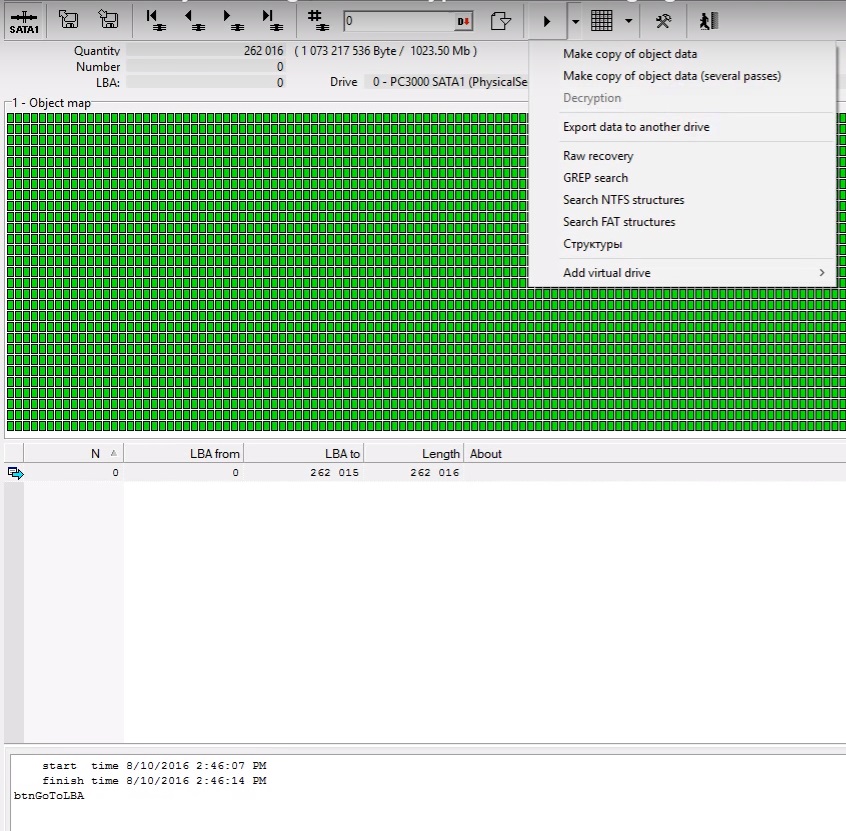
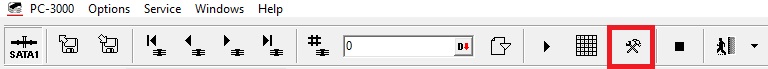
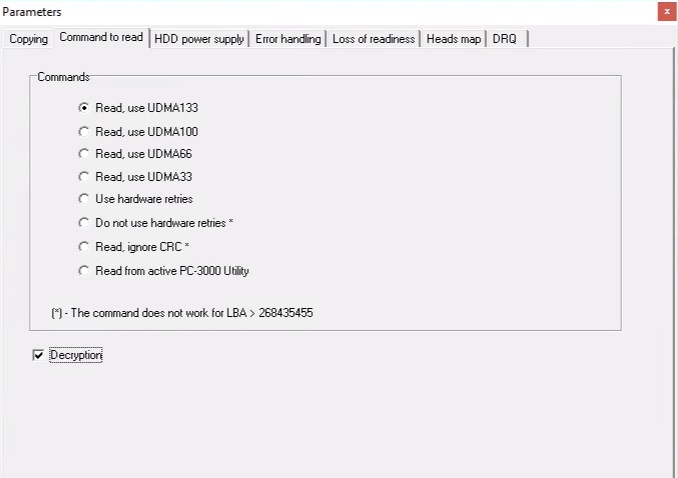
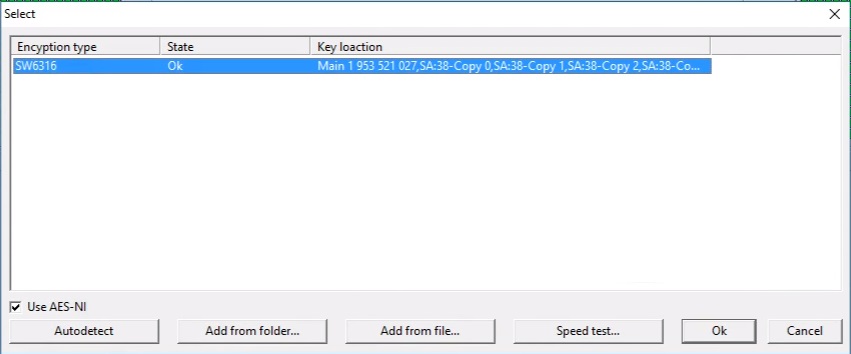
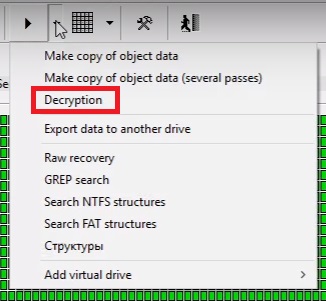
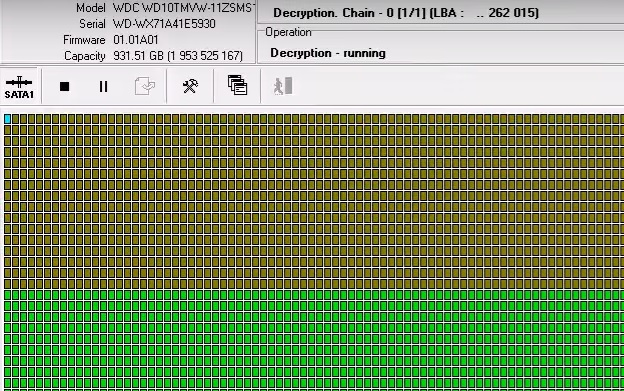
PC-3000 for HDD. Western Digital. The decryption of encrypted image.
This entry was posted in Articles, PC-3000 HDD and tagged encryption, MyBook, MyPassport, WD. Bookmark the permalink.





Great! thank you!
thank you!
Thank you!
i applied this method today, because i forgot to tick the box decryption and realized it after 30000000 sectors imaged :(.
Thanks a lot!!!
Thank you ACELAB Team! Great tool
Special thanks to Jackie Chan